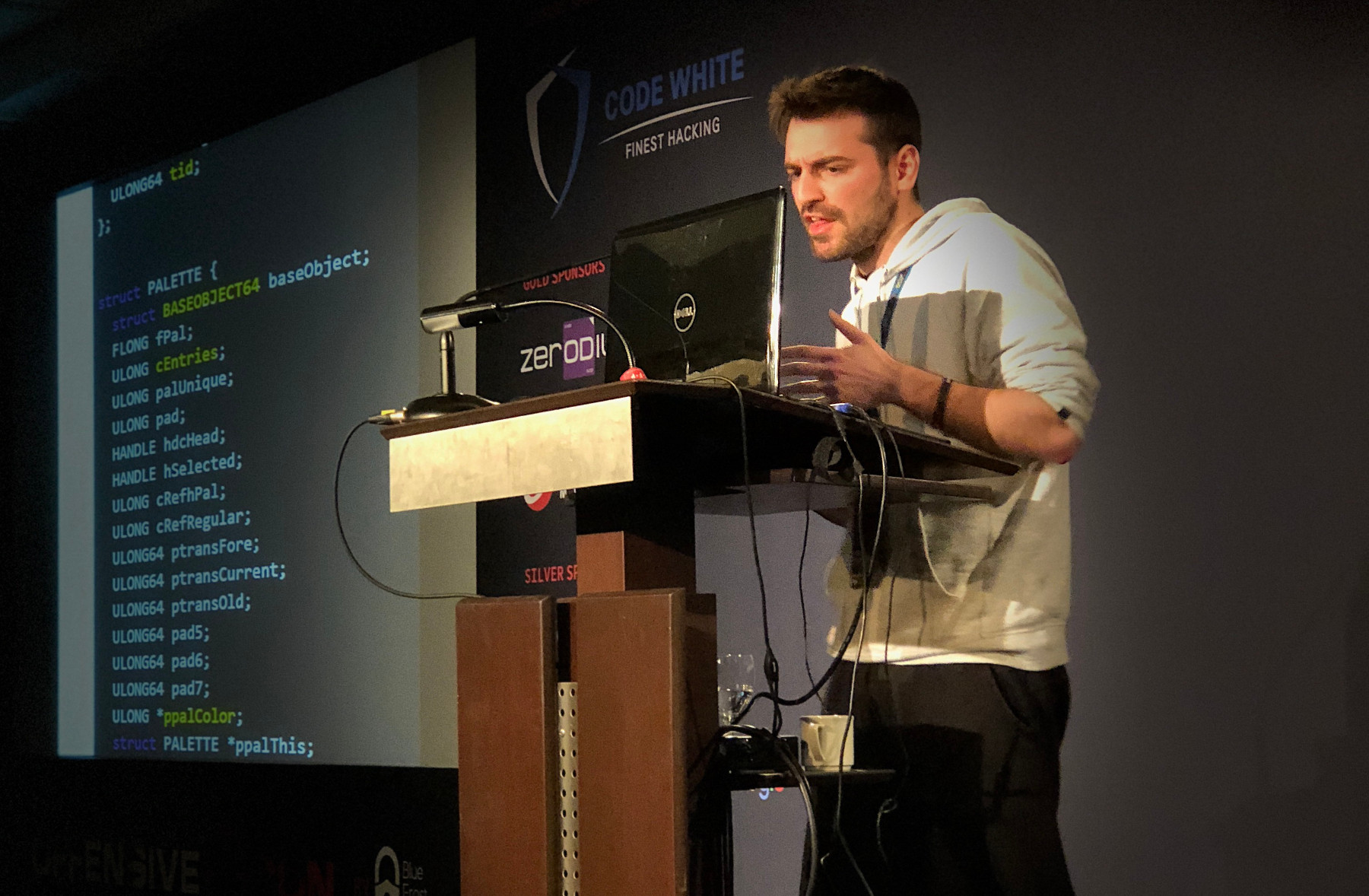
Windows 10 RS2/RS3 GDI data-only exploitation tales (OffensiveCon 2018)
Hello, I'm Nikos Sampanis, a security researcher working at CENSUS. On February 16th, 2018 I presented at OffensiveCon a talk with the title "Windows 10 RS2/RS3 GDI data-only exploitation tales". The presentation focused on a mitigation introduced in the Win32k component of Microsoft Windows to prevent the exploitation of memory corruptions in the session heap (due to GDI object abuse).
I realized that the mitigation exists when I tried to exploit a (re-surfaced) bug in Windows RS2. In the presentation, I introduced two methods to bypass this mitigation. The first approach was based on a public method which had a serious shortcoming, leading to a deadlocked exploit process. I explained in detail how we can wake up the deadlocked thread and escalate privileges from a user with low privileges to SYSTEM privileges.
The second method was the one I used to exploit the vulnerability in a Windows 10 RS3 context. Since the bug was patched in RS3, I wrote a driver that imitates the bug.
The driver and the two exploits (one for each method), are included in the released source code (available on GitHub).
In the final part of the presentation I reviewed the Win32kfilter system call filtering mechanism, and outlined a methodology for discovering new GDI-based exploitation primitives. I concluded with my thoughts on the future of GDI-based exploitation methods in Windows 10 RS4.
You may find the related presentation material below:
- Slides (PDF)
- Source Code (github repository)
I would like to thank the organizers of OffensiveCon 2018 for an excellent conference and I'm looking forward to next year's event!
